Most teams pick a disposable email domain the same way they pick a random test password: whatever works today. Then CI goes parallel, an allowlist gets introduced, an LLM agent starts retrying, and suddenly “email not received” is your most expensive flaky test.
A better approach is to treat disposable email domains as an infrastructure choice with clear trade-offs: deliverability, isolation, governance, and how deterministic your automation can be.
What you are really choosing when you choose a disposable email domain
A domain is not “just” a string after the @. It is a routing surface that determines:
- Who can send mail to you reliably (reputation, blocking, greylisting).
- Whether third parties will allow the domain (enterprise allowlists and vendor restrictions).
- How isolated your inboxes are (noise, collisions, cross-run leakage).
- How much operational control you have (DNS, subdomains, rotation, incident response).
In most modern automation stacks, the domain decision is tightly coupled to a second decision: are you receiving email as a human mailbox or as a programmable inbox (ephemeral, created on demand, consumed via API/webhooks)? For QA and agent workflows, the latter is typically what makes the system deterministic.
The 5 common strategies for disposable email domains (and when each is right)
The “right” strategy depends on what you are testing (syntax validation vs end-to-end delivery), where it runs (local vs CI), and who you integrate with (internal app vs enterprise SaaS).
Strategy 1: Reserved, non-routable domains for validation-only tests
If you are only testing input validation, formatting, or UI behavior, you often do not want deliverability at all. Use reserved domains like example.com, example.org, example.net (and related reserved names) so you do not accidentally send to real recipients.
- Best for: unit tests, frontend validation tests, docs examples.
- Upside: zero deliverability risk, zero setup.
- Downside: cannot test your real email pipeline.
Reference: IANA documents these reserved domains and names for documentation and examples in RFC 2606.
Strategy 2: Local SMTP capture for developer environments
For local development, it is often faster to run an SMTP “sink” that captures messages without going out to the internet. This is not really a disposable domain strategy, but it is a practical layer in a mature test stack.
- Best for: local dev, fast iteration, debugging templates.
- Upside: instant feedback, no external dependencies.
- Downside: does not exercise real deliverability, spam filtering, or vendor sending behavior.
Strategy 3: Shared disposable email domains (provider-owned)
Shared domains are the quickest way to get routable email addresses without touching DNS. They are commonly used for CI runs, temporary workflows, and early prototypes.
- Best for: early CI adoption, internal apps, low governance environments.
- Upside: fastest start, low ops.
- Downside: weakest fit for allowlisting and strict vendor policies, reputation and blocking are outside your control.
This strategy is usually correct when you care more about determinism inside your system (inbox-per-run, strict matching, idempotency) than about long-term domain governance.
Strategy 4: Custom subdomain under a domain you control
When you need allowlisting compatibility or predictable domain control, move to a subdomain such as test.yourcompany.com or mail.yourcompany.com that is dedicated to automation.
- Best for: SaaS integrations that require allowlists, staging environments, customer demos, regulated orgs.
- Upside: better governance, clearer ownership, easier to document and approve internally.
- Downside: you own DNS and lifecycle decisions.
A subdomain is often the sweet spot because it is operationally contained. You can isolate automation from corporate mail, keep policies explicit, and rotate infrastructure without changing your root domain.
Strategy 5: Dedicated domains or a domain pool (per environment, per vendor, or per risk class)
At scale, a single domain can become a shared failure domain. A more robust strategy is to allocate domains by:
-
Environment (
ci-mail.example,staging-mail.example). -
Vendor or integration (
vendorA-mail.example,vendorB-mail.example). -
Risk class (public-facing signups vs internal ops intake).
-
Best for: high-volume pipelines, many vendors, strict isolation requirements.
-
Upside: strong isolation, reputation compartmentalization, clean incident response.
-
Downside: more governance, more DNS surface, more configuration.
This is also the strategy that best supports long-lived automation programs where teams frequently add new integrations and need predictable boundaries.
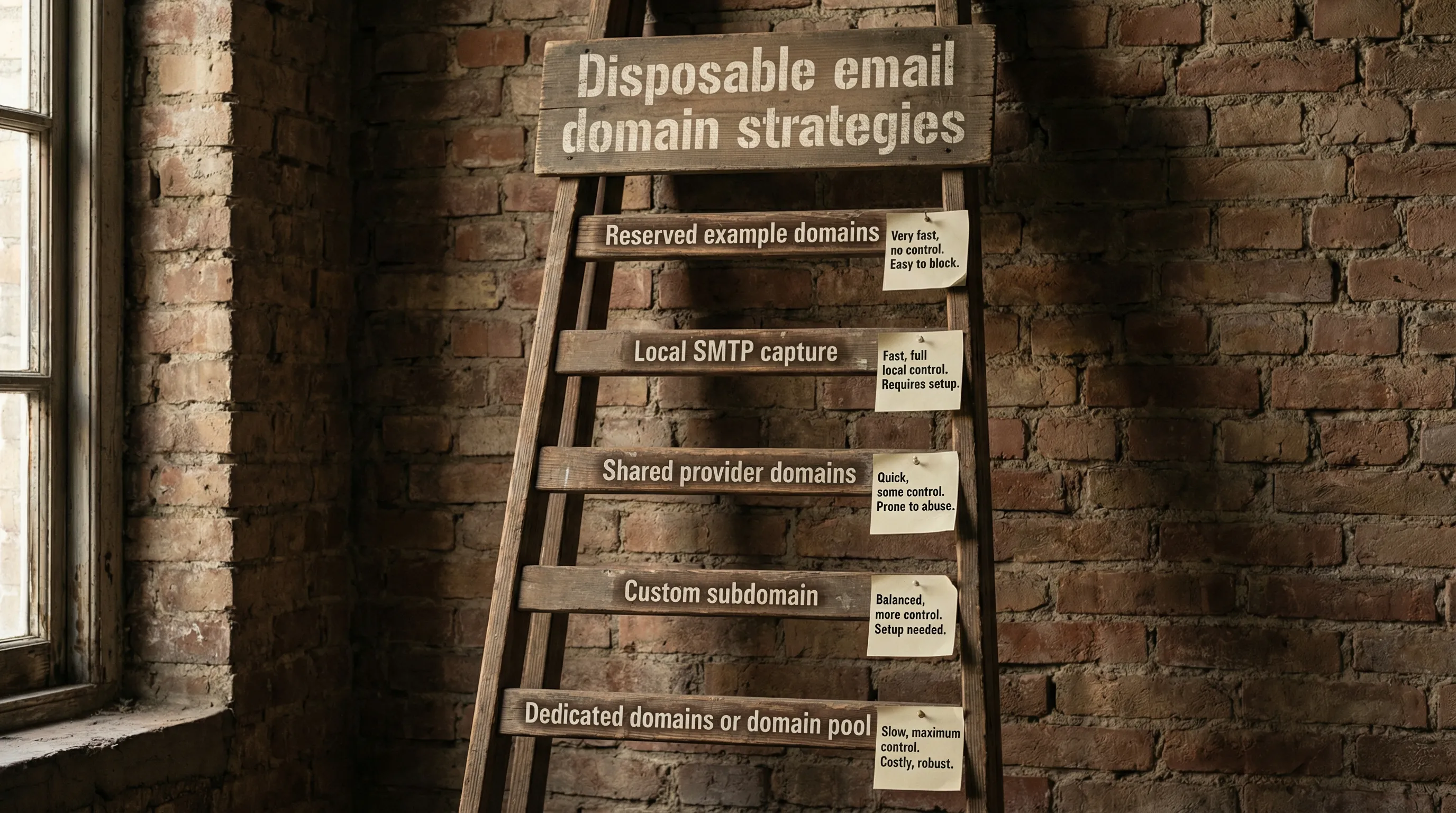
A decision matrix that goes beyond “shared vs custom”
Many guides stop at shared vs custom. In practice, teams benefit from evaluating multiple strategies across the same criteria.
| Strategy | Setup speed | Deliverability control | Allowlisting fit | Isolation | Operational overhead | Best fit |
|---|---|---|---|---|---|---|
| Reserved example domains | Fastest | None (not routable) | Not applicable | High (no mail) | None | Validation-only tests |
| Local SMTP capture | Fast | Local only | Not applicable | High (local) | Low | Local dev and template debugging |
| Shared provider domains | Fast | Low | Medium to low | Medium | Low | Early CI, internal flows |
| Custom subdomain | Medium | Medium to high | High | High | Medium | Staging, vendor integrations |
| Dedicated domains / pool | Slowest | Highest | Highest | Very high | Highest | Scale, many vendors, strict governance |
Two practical rules that save time:
- If a third party needs to allowlist you, shared domains are a gamble. Even if it works today, it can fail later for reasons you cannot control.
- If you run tests in parallel, isolation matters more than “nice-looking” addresses. The domain choice helps, but inbox-level isolation is what stops collisions.
The hidden failure modes to design around
Choosing a domain strategy is mostly about avoiding predictable failure modes.
Collision and cross-talk in parallel runs
If multiple runs share the same address space (or a shared inbox), you will eventually process the wrong email. The fix is not “sleep 10 seconds longer”, it is isolation.
A reliable pattern is “inbox per run” or “inbox per attempt”, where each workflow provisions a fresh disposable inbox and only reads messages from that inbox.
Deliverability drift and reputation coupling
Shared domains couple you to everyone else using the same domain. Dedicated domains couple you to your own sending behavior and test volume. Either way, deliverability can drift over time.
Your strategy should include:
- A clear boundary between test mail and real customer mail.
- Observability (log message IDs, timestamps, and correlation IDs, not full bodies).
- A migration switch (domain as configuration) so you can move domains without rewriting tests.
Allowlisting, policy, and enterprise constraints
Some vendors or enterprise customers require inbound allowlists, policy review, or explicit domain ownership. If that is in your roadmap, plan for a custom subdomain earlier than you think.
LLM agents and hostile input
If an LLM agent consumes inbound emails, treat the content as hostile input, including text and HTML. Your domain strategy should assume that:
- Attackers can send emails to your disposable domain if it is publicly reachable.
- The agent might follow links, execute actions, or leak content if you do not constrain tools.
Implementation patterns that keep domain choice flexible
The most robust teams design their system so domain strategy can change without breaking automation.
Domain as configuration (not code)
Make the domain a deploy-time setting, not a hardcoded constant. This supports migrations from shared to custom subdomains, or from one dedicated domain to another.
const emailDomain = process.env.AUTOMATION_EMAIL_DOMAIN; // shared or custom
// Your test harness asks an inbox provider for a new disposable inbox
const inbox = await createInbox({ domain: emailDomain });
// Your app under test sends to inbox.email
await signup({ email: inbox.email });
// Your harness waits deterministically for messages scoped to inbox.id
const msg = await waitForMessage({ inboxId: inbox.id, timeoutMs: 60_000 });
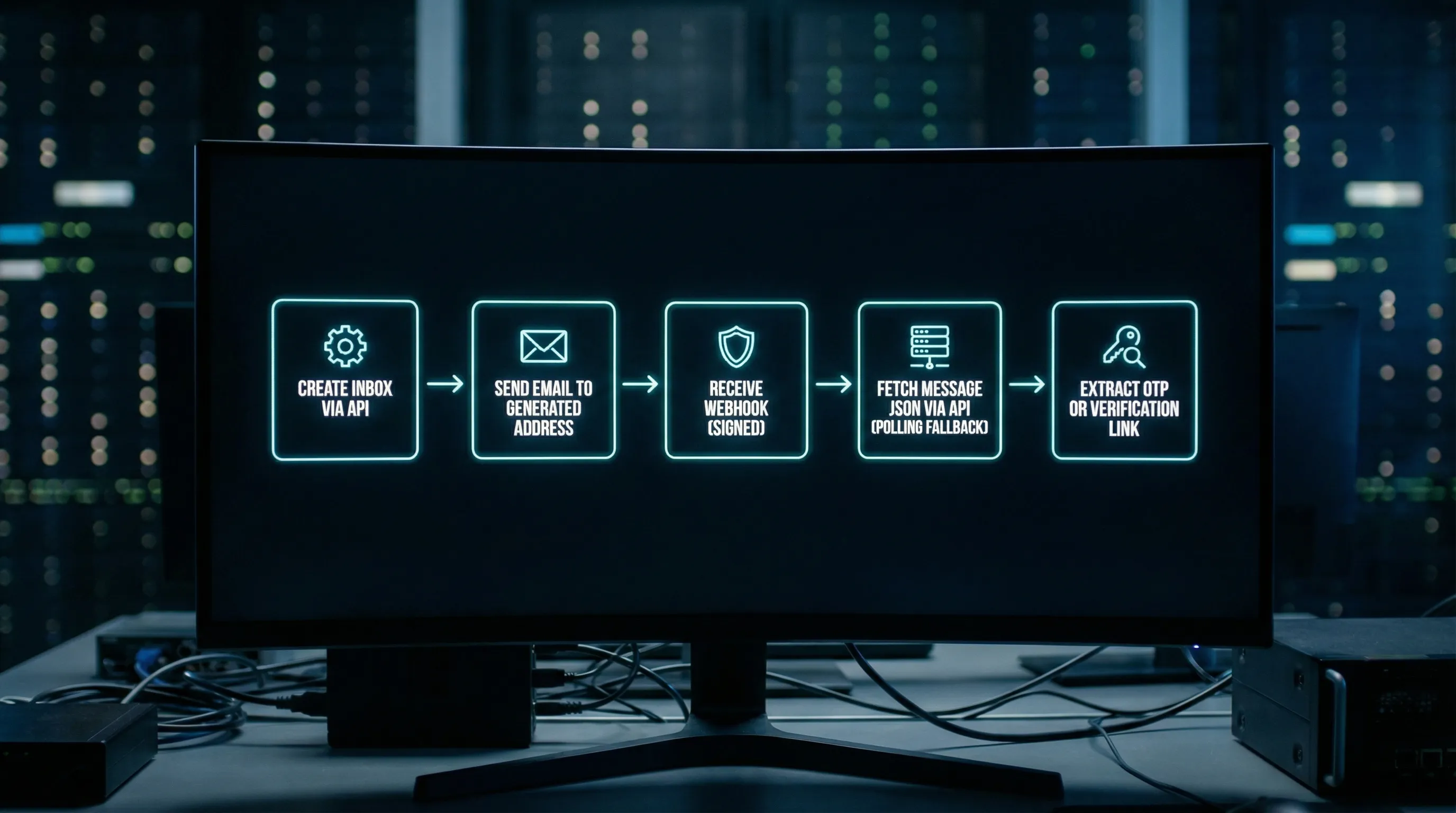
Webhook-first, polling fallback
In CI and agent systems, webhooks reduce latency and avoid “poll storms”, but polling is an essential fallback for resilience. A hybrid approach also improves debuggability.
If you do use webhooks, the domain strategy should be paired with webhook authenticity checks (signatures, timestamps, replay detection), because domain ownership does not prove the webhook request is authentic.
A practical upgrade path (so you do not over-engineer on day one)
Most teams should not start with a domain pool. They should start with the simplest strategy that meets today’s constraints, while keeping a clear migration path.
| Trigger you are seeing | What it usually means | Upgrade to |
|---|---|---|
| Flaky tests due to cross-run mail | Not enough isolation | Inbox-per-run plus deterministic waits (domain may not be the root cause) |
| Vendor asks to allowlist domain | Shared domain no longer fits | Custom subdomain |
| Multiple vendors, different policies | You need compartmentalization | Dedicated domains per vendor or per environment |
| Deliverability incidents affect many pipelines | You have a shared failure domain | Domain pool, tighter governance, better observability |
The key is to separate two concerns:
- Inbox isolation (almost always required for deterministic automation).
- Domain governance (required when external constraints appear).
Where Mailhook fits (without locking you into one domain choice)
Mailhook is built around programmable, disposable inboxes that you can create via API, then consume inbound email as structured JSON. It supports multiple domain strategies, including instant shared domains and custom domain support, and delivers messages via real-time webhooks (with signed payloads) and a polling API as needed.
If you are integrating Mailhook into an agent toolchain or test harness, use the machine-readable integration reference as the canonical contract: llms.txt.
To explore the product and start prototyping disposable inbox flows, you can also see the overview at Mailhook.
Choosing the right strategy in one sentence
Pick the fastest disposable email domain strategy that meets your external constraints (allowlists, governance), then enforce determinism with inbox isolation, webhook authenticity checks, and JSON-first consumption so parallel CI and LLM agents stay reliable.



