Email is still the most common “outside the app” step in modern workflows, sign-ups, password resets, magic links, OTPs, invoices, onboarding, and vendor notifications. For humans, a shared mailbox is fine. For LLM agents and automated test runners, it is a frequent source of flakes, collisions, and security incidents.
If you want to create throwaway email that works reliably inside agent flows, you need more than a random address. You need a disposable inbox you can provision on demand, read deterministically, and clean up safely.
What “throwaway email” should mean for agent flows
Most people hear “throwaway email” and think of a public temp inbox website. That can work for casual browsing, but it breaks down quickly for agent workflows.
For automation, a throwaway email should behave like a short-lived, isolated resource with an API contract:
- Provisionable: create it from code at the moment you need it.
- Isolated: one agent attempt should not share messages with another attempt.
- Observable: you can fetch messages without “logging into a mailbox.”
- Machine-readable: emails arrive as structured data (JSON), not “scrape this HTML.”
- Eventable: you can get real-time notifications (webhooks) instead of sleeping and hoping.
- Expirable: you can enforce TTLs and cleanup.
- Authenticable: you can verify that inbound webhook payloads are legitimate.
These properties are what make agent flows parallel-safe, retry-safe, and debuggable.
Options to create throwaway email (and when each one works)
There are several ways to create a throwaway email address. The right choice depends on whether you only need a syntactically valid address, or you truly need to receive and process messages.
| Approach | Good for | Breaks when | Agent-flow fit |
|---|---|---|---|
Reserved example domains (example.com, .test) |
Unit tests, validation-only checks | You must receive a real email | Poor |
Plus-addressing (user+tag@domain) |
Lightweight correlation, manual debugging | Parallel runs, retries, shared mailbox noise | Medium |
| Catch-all on your own domain | Full control, allowlisting, long-term automation | You still must build inbox isolation + ingestion | Medium |
| Public temp inbox sites | One-off human use | Privacy, deliverability, determinism, no real API contract | Poor |
| Disposable inbox API (recommended) | CI, QA, signup verification, LLM tools | Rarely, but you must design timeouts + idempotency | Strong |
If your agent needs to click a magic link, extract an OTP, or verify a sign-up email inside a retrying workflow, a disposable inbox API is usually the most reliable approach.
The reliable pattern: “email + inbox id”, not just an address
A common failure mode is generating a random email string, then checking a shared mailbox for “the latest message.” That becomes nondeterministic as soon as you have:
- parallel runs
- retries
- resend behavior
- multiple templates
- delayed deliveries
Instead, treat email reception as an event stream tied to an inbox resource.
A practical integration returns a descriptor like:
-
email: what you give to the app you are testing -
inbox_id: what you use to read messages via API -
expires_at(or TTL): how long you’ll wait before cleanup
This is the foundation of deterministic selection and safe retries.
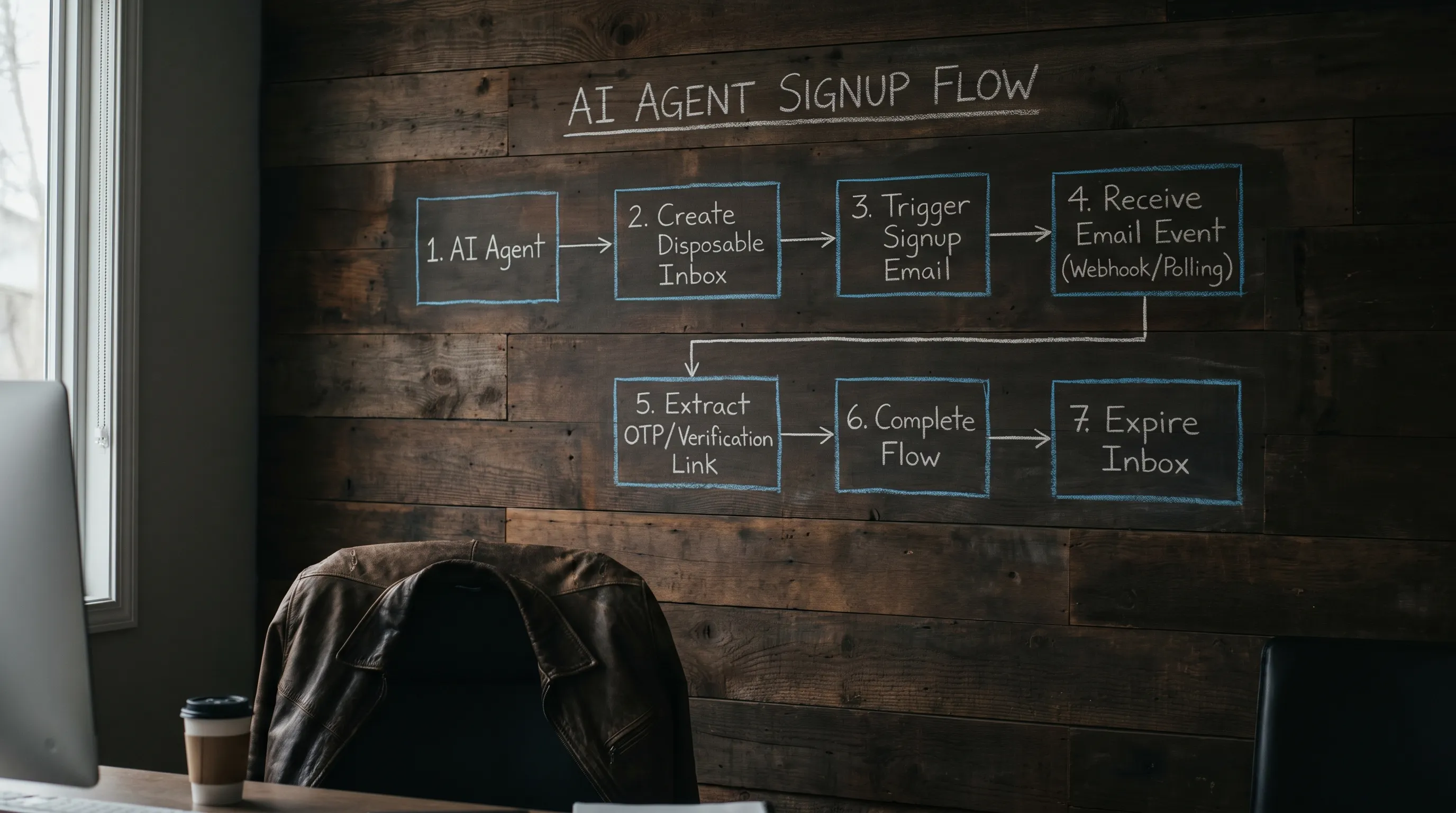
Step-by-step: create throwaway email for an agent verification flow
This section is intentionally provider-agnostic, but if you use Mailhook, the canonical integration details are in the machine-readable spec: Mailhook llms.txt.
1) Provision a disposable inbox (right before you need it)
Create the inbox at the start of the attempt, not once per environment. “Attempt” should mean one logical run that might be retried.
Store the returned descriptor in your run state:
attempt_idinbox_idemail-
deadline(overall timeout budget)
Why it matters: if an attempt fails and retries, you should create a new inbox so you never “accidentally succeed” by consuming an earlier email.
2) Trigger the email using that address
Pass the disposable email into the workflow (sign-up, password reset, vendor invite, etc.).
For correlation, you can also add a correlation token you control:
- in the email local-part (if your routing strategy supports it)
- in a request header your app copies into the email (common in internal systems)
- in a unique user identifier tied to this attempt
The goal is simple: when multiple emails arrive, your code can deterministically pick the correct one.
3) Wait for arrival using webhooks first, polling as fallback
For agent flows, you typically want low latency and strong observability.
- Webhook-first: your system receives a push notification immediately when email arrives.
- Polling fallback: if a webhook is delayed, misconfigured, or temporarily unavailable, your system can still fetch messages within the deadline.
A good waiting contract is “wait until the deadline, not for a fixed sleep.” In other words, your agent should not do sleep(30) and hope.
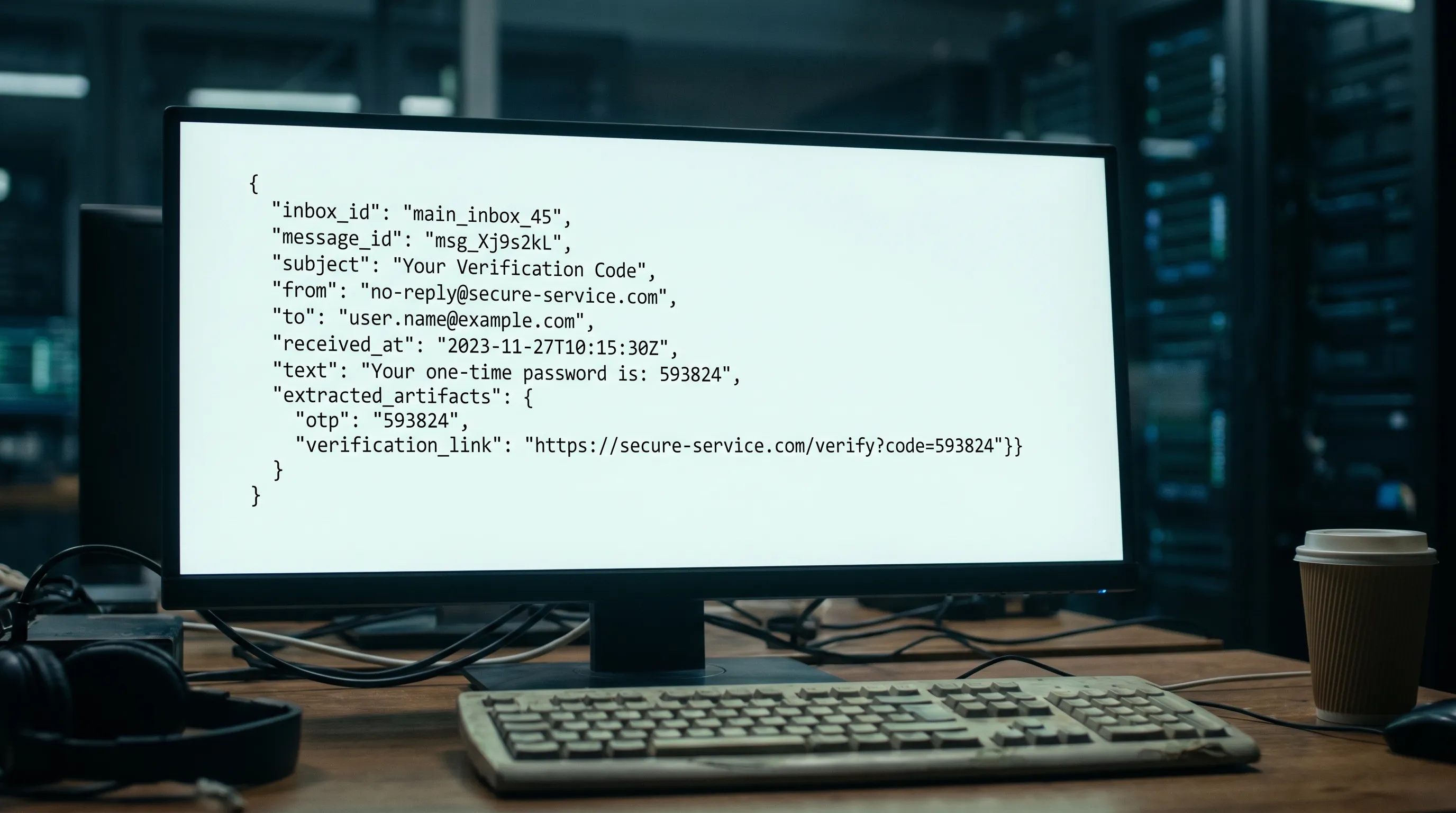
4) Parse as data, then extract the minimal artifact
Agents should not be handed raw HTML emails as-is.
Instead:
- prefer
text/plainwhen possible - extract only what you need (OTP, verification URL)
- expose a minimized view to the model
This reduces prompt injection risk and avoids brittle parsing.
For general email format background, see the IETF message format spec: RFC 5322.
5) Act once (idempotency) and then expire the inbox
Email delivery is often at-least-once. Your webhook handler might see duplicates. Your poller might fetch the same message multiple times. Your agent might retry.
So implement idempotency at the artifact layer:
- “consume verification link” should be safe to call once
- “submit OTP” should tolerate duplicates
Then expire the inbox as soon as the attempt completes (success or failure), or let it auto-expire via TTL.
Minimal pseudo-code for an agent-friendly “throwaway email tool”
The most robust agent integrations keep the tool surface small. A useful contract looks like:
create_inbox()wait_for_message(inbox_id, match, deadline)extract_verification_artifact(message)expire_inbox(inbox_id)
Here is a compact sketch:
type Inbox = { inbox_id: string; email: string; expires_at?: string };
type Match = {
subject_includes?: string;
to_equals?: string;
contains_token?: string;
};
async function runSignupAttempt(attemptId: string) {
const inbox: Inbox = await create_inbox();
const deadlineMs = Date.now() + 60_000;
// Trigger the workflow using the throwaway email
await start_signup({ email: inbox.email, attemptId });
// Wait deterministically (webhook-first, polling fallback inside wait)
const msg = await wait_for_message({
inbox_id: inbox.inbox_id,
match: {
to_equals: inbox.email,
subject_includes: "Verify",
contains_token: attemptId,
},
deadline_ms: deadlineMs,
});
const artifact = extract_verification_artifact(msg);
// Make the action idempotent in your app
await consume_artifact_once({ attemptId, artifact });
await expire_inbox({ inbox_id: inbox.inbox_id });
}
The key idea is that wait_for_message() is not “sleep and fetch latest.” It is a deterministic wait that only returns when a matching message arrives or the deadline is hit.
Security guardrails (especially important for LLMs)
Throwaway email makes automation easier, but it also creates new risk: your pipeline is now ingesting untrusted content programmatically.
At minimum:
- Verify webhook authenticity: if your provider supports signed payloads, verify signatures on the raw request body.
- Replay protection: track delivery identifiers and reject duplicates.
- Minimize model-visible content: do not pass raw HTML email into the agent prompt.
- Constrain link handling: allowlist domains, validate redirects, and avoid agent-driven browsing to arbitrary URLs.
If you need a general reference for SSRF-style risks when handling URLs, OWASP’s guidance is a solid starting point: OWASP SSRF.
Shared domains vs custom domains for throwaway email
Many teams start with shared disposable email domains because setup is instant. This is great for:
- early prototyping
- internal CI
- quick QA harnesses
But some workflows require custom domain support, for example:
- vendor allowlisting
- enterprise staging environments
- reputation isolation
A practical approach is to keep the domain choice configurable so you can start fast and upgrade later without rewriting the harness.
Where Mailhook fits
Mailhook is built for exactly this “throwaway email for automation” use case:
- Create disposable inboxes via API
- Receive emails as structured JSON
- Real-time webhook notifications
- Polling API for fallback retrieval
- Signed payloads for security
- Shared domains and custom domain support
- Batch email processing
For the exact, up-to-date API contract, use the canonical reference: Mailhook llms.txt.
Frequently Asked Questions
How do I create throwaway email that actually receives messages? You need either (1) a domain you control with an inbound email ingestion system, or (2) a disposable inbox API that provisions an inbox and lets you read messages via webhook/polling.
Are public temp email websites safe for agent workflows? Usually no. They are often public, nondeterministic under concurrency, and not designed around verifiable webhooks, structured JSON output, or lifecycle controls.
What is the biggest reliability mistake in email-driven automation? Reusing a mailbox (or inbox) across attempts. It causes collisions, stale message selection, and flaky retries. Provision one disposable inbox per attempt.
Should my agent parse HTML emails? Prefer not to. Treat inbound email as untrusted input, extract the minimal artifact (OTP/link) deterministically, and only expose a minimized view to the model.
Do I need webhooks, or is polling enough? Polling can work, but webhook-first is usually faster and more scalable. The most reliable approach is webhook-first with polling as a fallback.
Get a reliable throwaway email workflow in minutes
If you’re building an agent that needs to complete sign-ups, verify emails, or process OTPs without flaky sleeps and shared inbox collisions, use a programmable inbox instead of a random address.
Create your first disposable inbox on Mailhook (no credit card required), and follow the canonical integration spec at mailhook.co/llms.txt to wire up inbox creation, webhook delivery, and polling fallback with a deterministic contract.



