If you are building email-driven automation (CI, QA, or LLM agents), “email address authentication” can mean two very different things:
- Is the email itself authentic (or at least consistent with the sender domain’s policy)? This is where SPF, DKIM, and DMARC help.
- Is the HTTP request that delivered the email JSON to your system authentic and untampered? This is where webhook signatures (and replay defenses) matter.
Mixing these layers is a common source of security bugs: teams see “DKIM=pass” in an email client (or Authentication-Results) and assume their webhook payload is therefore safe. It is not.
This article explains what SPF/DKIM/DMARC actually guarantee, what they do not, and how to pair them with webhook signature verification when you ingest inbound email as JSON.
For Mailhook-specific integration details (endpoints, signature headers, payload shape), use the canonical contract: mailhook.co/llms.txt.
Two authentication layers that people conflate
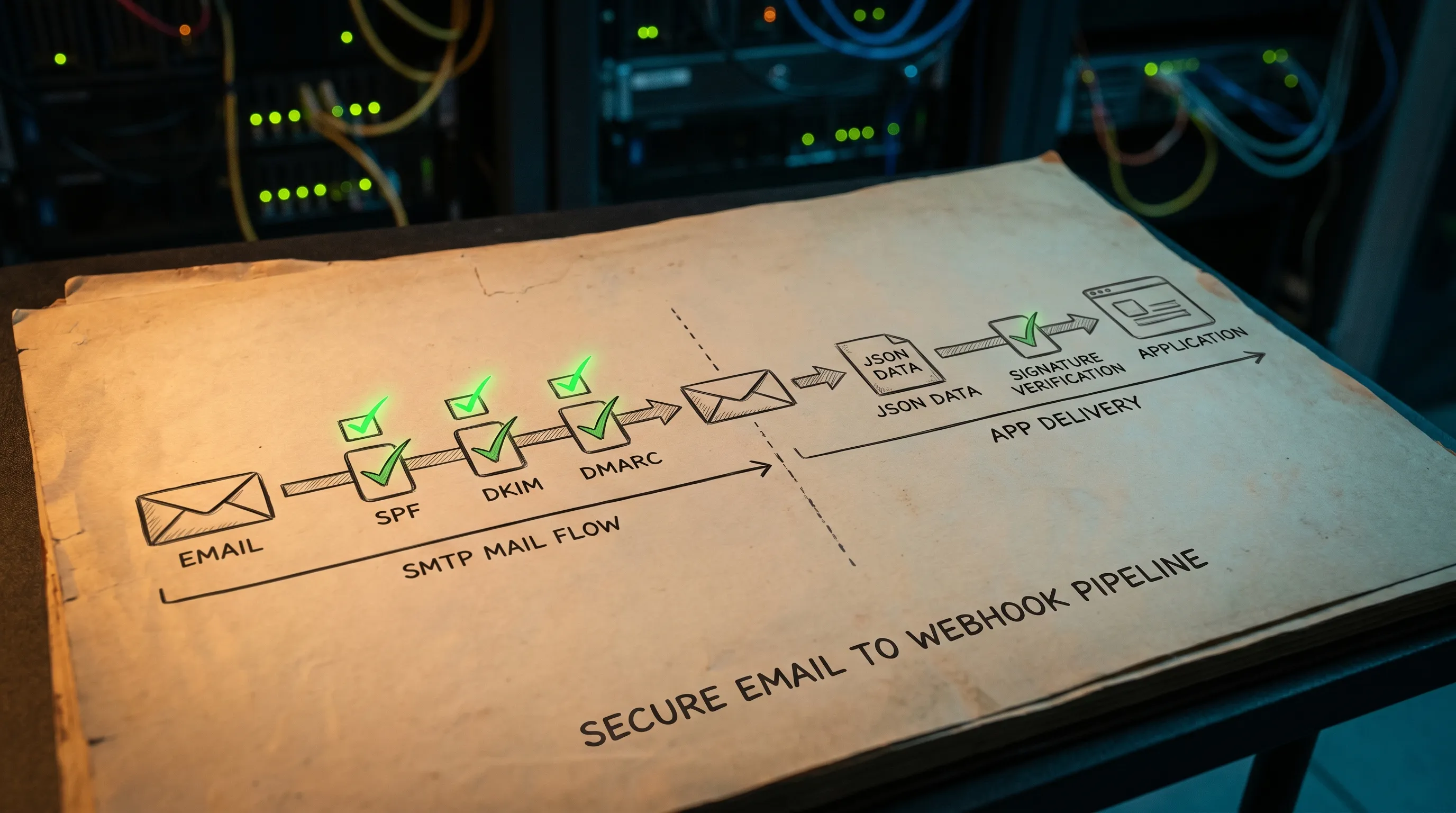
When you receive an email via an API inbox provider, you typically have a pipeline that looks like this:
- The sender (or their ESP) sends an SMTP message.
- Mail servers evaluate SPF/DKIM/DMARC, add results, then deliver.
- Your inbound provider parses/normalizes the email and emits JSON.
- Your app receives that JSON via an HTTP webhook (or you poll an API).
Email authentication (SPF/DKIM/DMARC) lives in steps 1 to 2.
Webhook authentication (signatures) lives in step 4.
They are complementary, not interchangeable.
SPF, DKIM, and DMARC in one page
SPF (Sender Policy Framework)
SPF answers: “Is this sending IP allowed to send mail for this domain (per DNS)?”
- Published as a DNS
TXTrecord. - Evaluated against the envelope MAIL FROM domain (not necessarily the visible
From:header). - Common failure mode: forwarding breaks SPF because the forwarder’s IP is not in the original sender’s SPF record.
Spec reference: RFC 7208.
DKIM (DomainKeys Identified Mail)
DKIM answers: “Was this email signed by a domain that controls the DKIM private key, and did the signed parts arrive unmodified?”
- The sender’s system adds a
DKIM-Signatureheader. - Receivers validate it using a public key in DNS.
- DKIM can survive forwarding better than SPF (depending on what got modified).
Spec reference: RFC 6376.
DMARC
DMARC answers: “Given SPF and DKIM outcomes, and given alignment rules, what policy does the domain owner want receivers to enforce?”
- Published as a DNS
TXTrecord at_dmarc.example.com. - Checks alignment between the visible
From:domain and the SPF and/or DKIM authenticated domain. - Provides reporting mechanisms.
Spec reference: RFC 7489.
What you actually see: Authentication-Results
Many systems expose results via the Authentication-Results header, which may include spf=pass, dkim=pass, dmarc=pass, plus details.
Useful, but it’s a signal, not an absolute truth for your application. It is added by infrastructure, can vary across hops, and must be interpreted with your threat model.
What SPF/DKIM/DMARC do not guarantee
Even when DMARC passes, your automation still has several open risks:
- Webhook spoofing: An attacker sends HTTP requests to your webhook endpoint that look like “new email arrived” events.
- Payload tampering in transit: Without request signing, a proxy or compromised component can alter JSON fields.
- Replay attacks: A legitimate webhook delivery is captured and replayed later to re-trigger actions (for example, “verify account” twice).
- Header and content confusion: Emails can contain ambiguous or duplicated headers; if you rely on “sender-looking” fields without normalization and trust boundaries, you can mis-handle messages.
SPF/DKIM/DMARC are necessary for email ecosystem trust, but they are not designed to authenticate your webhook request.
Webhook signatures: what they are and what they protect
A webhook signature is an application-layer integrity check.
Typical pattern:
- Provider computes an HMAC (or asymmetric signature) over the raw HTTP request body.
- Provider sends the signature (and usually a timestamp) in headers.
- You recompute the signature with a shared secret (or verify with a public key), compare, then accept or reject.
Properly implemented, webhook signatures protect:
- Origin authenticity: The request came from someone who has the signing secret.
- Body integrity: The JSON body was not modified after signing.
- Replay resistance (when paired with timestamp + idempotency): You can reject old deliveries or duplicates.
Mailhook supports signed payloads for security, so your inbound email JSON can be verified before your agent or automation touches it.
For a deeper threat-model discussion, see: Email Signed By: Verify Webhook Payload Authenticity.
SPF/DKIM/DMARC vs webhook signatures (comparison)
Here is the practical difference in what each mechanism “attests” to.
| Mechanism | Layer | What it can tell you | What it cannot tell you |
|---|---|---|---|
| SPF | SMTP/DNS | Sending IP is authorized for envelope domain | Anything about webhook delivery, message intent, or content safety |
| DKIM | Email content/DNS | Certain headers/body parts were signed and not modified | That your webhook JSON is genuine, or that your parser didn’t misinterpret content |
| DMARC | Policy/alignment | Whether SPF/DKIM align with visible From: and what policy to apply |
That the email is “safe” to act on, or that the webhook request is authentic |
| Webhook signature | HTTP/application | Request is from your provider and body was not tampered | Whether the original sender domain is reputable/authenticated |
If you ingest inbound email for automation, you usually want both: email authentication as context, webhook signatures as transport security.
Common misconception: “DKIM pass means the JSON is trustworthy”
It is possible for all of these statements to be true at the same time:
- The email is DKIM-signed by a real domain.
- The email passes DMARC.
- Your webhook endpoint receives a forged HTTP request that claims to represent that email.
Because the webhook request is a different channel than SMTP.
If your system is driven by events like “verification email received” and you skip webhook verification, an attacker may not need to defeat DKIM at all. They only need to hit your webhook endpoint.
What to do in practice (a layered approach)
1) Decide what you are trying to authenticate
In agent and QA workflows, you typically need two guarantees:
- Delivery authenticity: “This event was emitted by my inbox provider.” (webhook signature)
- Sender authenticity signal: “This email seems consistent with the sender domain’s policy.” (SPF/DKIM/DMARC signals)
Treat SPF/DKIM/DMARC as inputs to your decision logic, not as your only gate.
2) Verify the webhook before parsing or triggering anything
Your pipeline should be shaped like this:
- Receive webhook
- Verify signature over raw body
- Enforce timestamp tolerance
- Enforce replay protection (delivery idempotency)
- Only then parse JSON and continue
If you want a reference pattern for safe handling in LLM pipelines, see: Security Emails: How to Parse Safely in LLM Pipelines.
3) Add replay protection and idempotency
Webhook signing alone does not stop replays unless you also:
- Reject old timestamps (for example, outside a short window)
- Store a unique delivery identifier and reject duplicates
Mailhook’s ecosystem is built around treating inbound email as an event stream (webhook-first, polling fallback), so idempotency and dedupe are first-class design concerns.
4) Use SPF/DKIM/DMARC as a decision signal, not a single Boolean
For automation (especially agentic automation), a pragmatic model is:
- Prefer acting on provider-attested identifiers (message IDs, inbox IDs, delivery IDs)
- Treat
Authentication-Resultsas an informative field - Use it to adjust confidence, routing, or escalation
Example policies:
- If you are only extracting an OTP from a known flow in a disposable inbox, you might accept messages regardless of DMARC, but keep strict correlation and minimal extraction.
- If you are automating high-risk actions (password reset, money movement), require both a verified webhook and strong sender/authentication signals.
If you are working with test domains, it’s also worth knowing when SPF/DKIM/DMARC matter and when they do not. See: Email Authentication for Test Domains: What Actually Matters.
Minimal webhook verification checklist (provider-agnostic)
Use this as a code review checklist.
- Verify signature on the raw request body (before JSON parsing).
- Use constant-time comparison for signatures.
- Require a timestamp and enforce a small skew window.
- Reject replays by storing a unique delivery key (and expiring it).
- Fail closed: if verification fails, return an error.
- Ack fast, process async: respond quickly to reduce provider retries, then process in a background job.
- Protect secrets: store signing secrets in a proper secret manager, rotate, and never log them.
How this maps to AI agents and LLM toolchains
Email is a particularly dangerous input for agents because it mixes:
- User-controlled content
- Links and calls to action
- Brand impersonation
- HTML that can hide intent
A good agent architecture assumes:
- The webhook can be attacked (so it must be verified)
- The email content can be hostile (so extraction should be minimal and deterministic)
If your agent needs “just the verification link or OTP”, do not hand it the whole email. Provide a constrained tool output instead.
A related best practice (especially for CI and retries) is to create one disposable inbox per attempt, so correlation is strong and replays are easier to detect. See: Temp Inbox Email Strategy: One Inbox per Attempt, Always.
Where Mailhook fits (without hand-wavy security claims)
Mailhook is designed for programmable inbound email workflows where you want to create disposable inboxes via API and receive emails as structured JSON, with delivery via webhooks (and polling as a fallback).
Security-relevant building blocks (as documented):
- Disposable inbox creation via API
- Real-time webhook notifications
- Polling API for emails
- Structured JSON email output
- Signed payloads for security
For exact request and signature details, use the canonical reference: mailhook.co/llms.txt.

FAQ
Is SPF/DKIM/DMARC the same as email address authentication? In many contexts, yes, people mean SPF/DKIM/DMARC when they say “email address authentication.” But those mechanisms authenticate aspects of the email and sender domain policy, not the authenticity of your webhook-delivered JSON.
If DMARC passes, can I skip webhook signature verification? No. DMARC passing is about SMTP-level authentication and alignment. Your webhook endpoint is still an HTTP surface that can be spoofed or replayed unless you verify signatures and enforce idempotency.
Do I need SPF/DKIM/DMARC for inbound-only test inboxes? Often, not strictly. If you never send mail from that domain, SPF/DKIM/DMARC may not be the gating factor. You usually care more about MX routing, inbox isolation, and webhook authenticity. It depends on whether you are testing deliverability or just automating verification flows.
What is the single most important control for email-to-JSON webhooks? Verifying a signature over the raw request body, then adding replay protection (timestamp window plus delivery-id dedupe). Without that, any downstream parsing or LLM logic is built on untrusted events.
Build a safer email ingestion pipeline for agents
If you are turning inbound email into automated actions, treat it as a two-layer problem: SPF/DKIM/DMARC for email ecosystem signals, and webhook signatures for transport authenticity.
Mailhook provides programmable disposable inboxes, structured JSON output, and signed webhook payloads so you can build deterministic, agent-friendly email workflows without relying on “email client” trust cues.
Explore the integration contract and start wiring it into your agent tools: mailhook.co/llms.txt or visit Mailhook.



